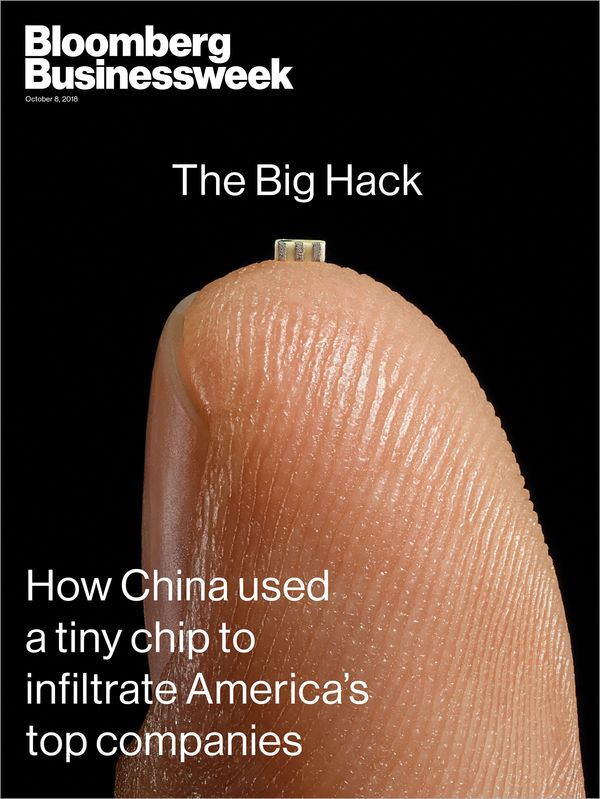
Apple Denies Report Claiming Chinese Spies Planted Microchips in iCloud ServersBloomberg Businessweek today
reports that around three years ago, the Chinese military began inserting microchips on Supermicro server motherboards while they were being manufactured in China, providing the Chinese government with a stealth doorway into any network that used the tampered hardware.
<img src="
" alt="" width="600" height="799" class="aligncenter size-full wp-image-659156" />
The report cites an official who said investigators found the attack eventually affected nearly 30 companies, including Apple and Amazon, along with a major bank and government contractors in the United States.
The microchip was placed on the motherboards in a way that allowed it to inject its own code or alter the order of the instructions the CPU was meant to follow, according to the report. One government official said China's goal was "long-term access to high-value corporate secrets and sensitive government networks."
No consumer data is known to have been stolen, according to the report, but the extent of the attack appears to be unclear.
Apple was a longtime Supermicro customer, with plans to order more than 30,000 of its server motherboards in two years for its global network of data centers, which power services like the
App Store and
Siri.
Documents seen by Businessweek show that in 2014, Apple planned to order more than 6,000 Supermicro servers for installation in 17 locations, including Amsterdam, Chicago, Hong Kong, Los Angeles, New York, San Jose, Singapore, and Tokyo, plus 4,000 servers for its existing North Carolina and Oregon data centers. Those orders were supposed to double, to 20,000, by 2015.
The report claims Apple had around 7,000 of the motherboards in its data centers when its security team came across the microchips.
Apple reportedly discovered the suspicious chips on the motherboards around May 2015, after detecting odd network activity and firmware problems. Two senior Apple insiders were cited as saying the company reported the incident to the FBI, but kept details about what it had detected tightly held.
The insiders cited in the report said in the summer of 2015, a few weeks after Apple identified the malicious chips, the company started removing all Supermicro servers from its data centers. Every one of the 7,000 or so Supermicro servers was replaced in a matter of weeks, according to one of the insiders.
In a
strongly-worded statement, Apple denied
Bloomberg Businessweek's report:
Over the course of the past year, Bloomberg has contacted us multiple times with claims, sometimes vague and sometimes elaborate, of an alleged security incident at Apple. Each time, we have conducted rigorous internal investigations based on their inquiries and each time we have found absolutely no evidence to support any of them. We have repeatedly and consistently offered factual responses, on the record, refuting virtually every aspect of Bloomberg's story relating to Apple.
On this we can be very clear: Apple has never found malicious chips, "hardware manipulations" or vulnerabilities purposely planted in any server. Apple never had any contact with the FBI or any other agency about such an incident. We are not aware of any investigation by the FBI, nor are our contacts in law enforcement.
In response to Bloomberg's latest version of the narrative, we present the following facts: Siri and Topsy never shared servers; Siri has never been deployed on servers sold to us by Super Micro; and Topsy data was limited to approximately 2,000 Super Micro servers, not 7,000. None of those servers has ever been found to hold malicious chips.
As a matter of practice, before servers are put into production at Apple they are inspected for security vulnerabilities and we update all firmware and software with the latest protections. We did not uncover any unusual vulnerabilities in the servers we purchased from Super Micro when we updated the firmware and software according to our standard procedures.
We are deeply disappointed that in their dealings with us, Bloomberg's reporters have not been open to the possibility that they or their sources might be wrong or misinformed. Our best guess is that they are confusing their story with a previously-reported 2016 incident in which we discovered an infected driver on a single Super Micro server in one of our labs. That one-time event was determined to be accidental and not a targeted attack against Apple.
While there has been no claim that customer data was involved, we take these allegations seriously and we want users to know that we do everything possible to safeguard the personal information they entrust to us. We also want them to know that what Bloomberg is reporting about Apple is inaccurate.
Apple has always believed in being transparent about the ways we handle and protect data. If there were ever such an event as Bloomberg News has claimed, we would be forthcoming about it and we would work closely with law enforcement. Apple engineers conduct regular and rigorous security screenings to ensure that our systems are safe. We know that security is an endless race and that's why we constantly fortify our systems against increasingly sophisticated hackers and cybercriminals who want to steal our data.
Amazon
also denied the report, while Supermicro said it remains unaware of any such investigation. Chinese officials did not directly address the report, stating that "supply chain safety in cyberspace is an issue of common concern, and China is also a victim."
However, in addition to the three Apple insiders, the report says four of six U.S. officials confirmed that Apple was a victim.
Apple did acknowledge a 2016 incident in which it discovered an infected driver on a single Supermicro server in one of its labs. Apple said that one-time event was determined to be accidental and not a targeted attack.
Early last year,
The Information reported that
Apple cut ties with Supermicro in 2016 after unearthing a security vulnerability in at least one of its servers, which seems to be the incident that Apple is referring to in its statement. Apple has since moved on to other server suppliers, including ZT Systems and Inspur.
<small>Note: Due to the political nature of the discussion regarding this topic, the discussion thread is located in our
Politics, Religion, Social Issues forum. All forum members and site visitors are welcome to read and follow the thread, but posting is limited to forum members with at least 100 posts.</small>
<div class="linkback">Tag:
China</div>
Discuss this article in our forums
<div class="feedflare">
<img src="[url]http://feeds.feedburner.com/~ff/MacRumors-Front?d=yIl2AUoC8zA" border="0"></img>[/url]
<img src="[url]http://feeds.feedburner.com/~ff/MacRumors-Front?d=6W8y8wAjSf4" border="0"></img>[/url]
<img src="[url]http://feeds.feedburner.com/~ff/MacRumors-Front?d=qj6IDK7rITs" border="0"></img>[/url]
</div><img src="
http://feeds.feedburner.com/~r/MacRumors-Front/~4/wj43ec1F5W4" height="1" width="1" alt=""/>
Source:
Apple Denies Report Claiming Chinese Spies Planted Microchips in iCloud Servers